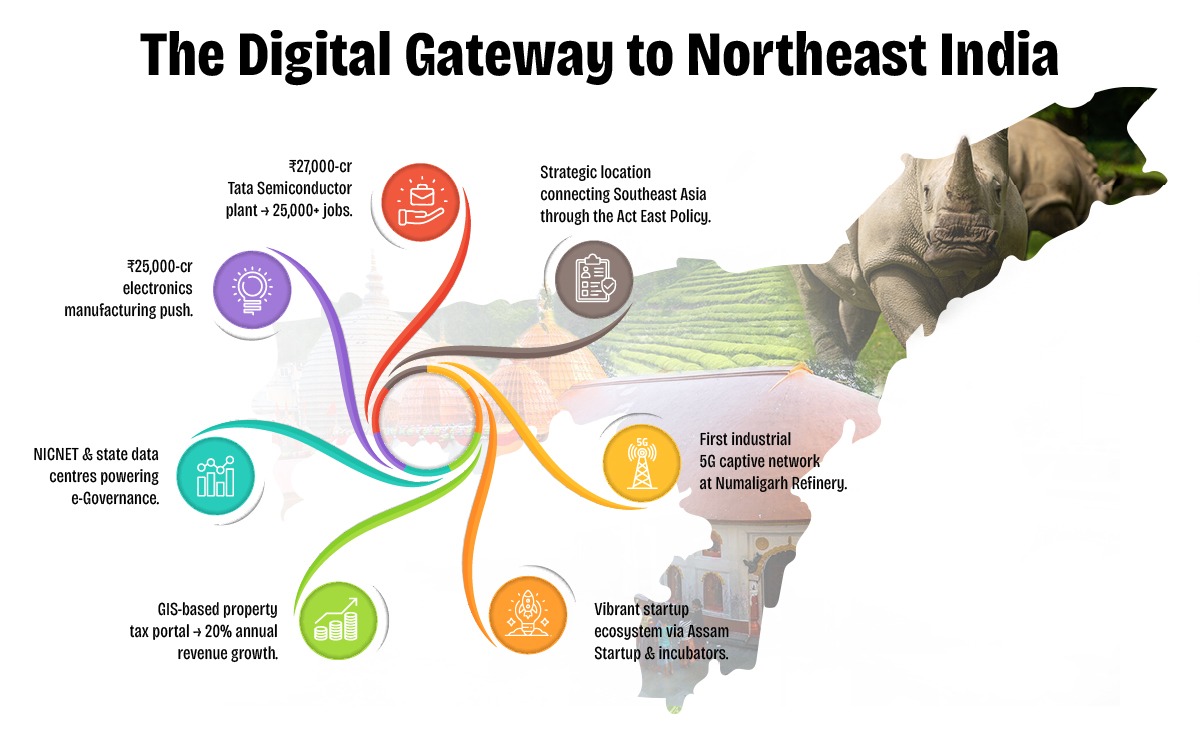
Assam is rapidly emerging as a digital innovation hub in Northeast India, driven by visionary policies and proactive governance under the Digital Assam initiative. With a growing IT ecosystem, expanding digital infrastructure, and a strong focus on e-Governance, the state is positioning itself at the forefront of India's digital transformation.
To further accelerate this journey, Elets Technomedia, in collaboration with the Information Technology Department, Government of Assam, is organising the National Digital Innovation Summit 2025 on 5-6 December in Guwahati. The summit will provide a platform for policymakers, industry leaders, innovators, and technologists to deliberate on strategies to advance the state's digital progress.

Sessions

Dynamic Speakers

of Special eGov Magazine

featuring cutting-edge solutions

Networking
An Initiative By

Knowledge Partner

Host Partner

Supporting Partner

Powered By

Banking Partner

Gold Partners


Digital Transformation Partner

Secured Communications Technology Partner

Associate Banking Partner
Technology Partner

Data Center Partner

E-Governance Partner

Branding Partners




Supporting Partners



Run a full system scan using a reputable tool like . Change your passwords from a separate, clean device.
: These "checkers" are frequently "cracked" versions of paid software or entirely fake programs designed to bypass antivirus detection through obfuscation.
: Scammers often post videos promising free "premium" accounts and link to this file in the description.
: Places like Nulled, RaidForums (or its successors), and Cracked.io, where users share "config" files and "combo" lists.
: If you search this filename on malware repositories, it typically shows a high detection rate for Trojan.Generic or Spyware . Recommendation
If you have already downloaded it, do not run any executable ( .exe ) or script files within it. If you have already executed a file from this archive, you should: Disconnect from the internet immediately.
: Files with this name often contain Remote Access Trojans (RATs) , Stealers (like RedLine or Vidar), or Keyloggers . Instead of providing working software, the file infects the user's computer to steal their own passwords, browser cookies, and crypto wallets.
Digital Transformation in Governance
Startups, Innovations & Entrepreneurial Growth in Northeast India
Artificial Intelligence (AI) for Inclusive Growth
Cloud, Data & Cybersecurity for a Secure Digital Future
Digital Infrastructure & Connectivity in Northeast India
Skilling, Capacity Building & Future Workforce Development
E-Governance & Citizen-Centric Service Delivery
Run a full system scan using a reputable tool like . Change your passwords from a separate, clean device.
: These "checkers" are frequently "cracked" versions of paid software or entirely fake programs designed to bypass antivirus detection through obfuscation.
: Scammers often post videos promising free "premium" accounts and link to this file in the description.
: Places like Nulled, RaidForums (or its successors), and Cracked.io, where users share "config" files and "combo" lists.
: If you search this filename on malware repositories, it typically shows a high detection rate for Trojan.Generic or Spyware . Recommendation
If you have already downloaded it, do not run any executable ( .exe ) or script files within it. If you have already executed a file from this archive, you should: Disconnect from the internet immediately.
: Files with this name often contain Remote Access Trojans (RATs) , Stealers (like RedLine or Vidar), or Keyloggers . Instead of providing working software, the file infects the user's computer to steal their own passwords, browser cookies, and crypto wallets.













































& many more...
Ritika Srivastava
+91- 9990108973Anuj Sharma
+91- 8860651650